Businesses large and small create and manage large volumes of data. These data are vital to the survival and continued operation of the business. Having a data backup and recovery system is imperative and a crucial element of disaster recovery plan businesses should have in place to mitigate losses.
Backup and Recovery describes the process of creating and storing copies of data that can be used to protect organizations against data loss.The copy of data are stored on separate media like external drives, a disk storage system, tape drive or in public and private cloud container. The alternate medium can be in the same location as the primary data or at a remote location. The possibility of natural disasters may justify having copies of data at remote locations.
When disaster strikes, whether physical or virtual, having a data backup and recovery system can mean the difference between inconvenience and catastrophe. These are some of the events that can cause data loss or corruption:
- Human error – accidental deletion of files.
- Hacking, viruses and malware.
- Machine or hardware failure.
- Power failure.
- Natural disasters.
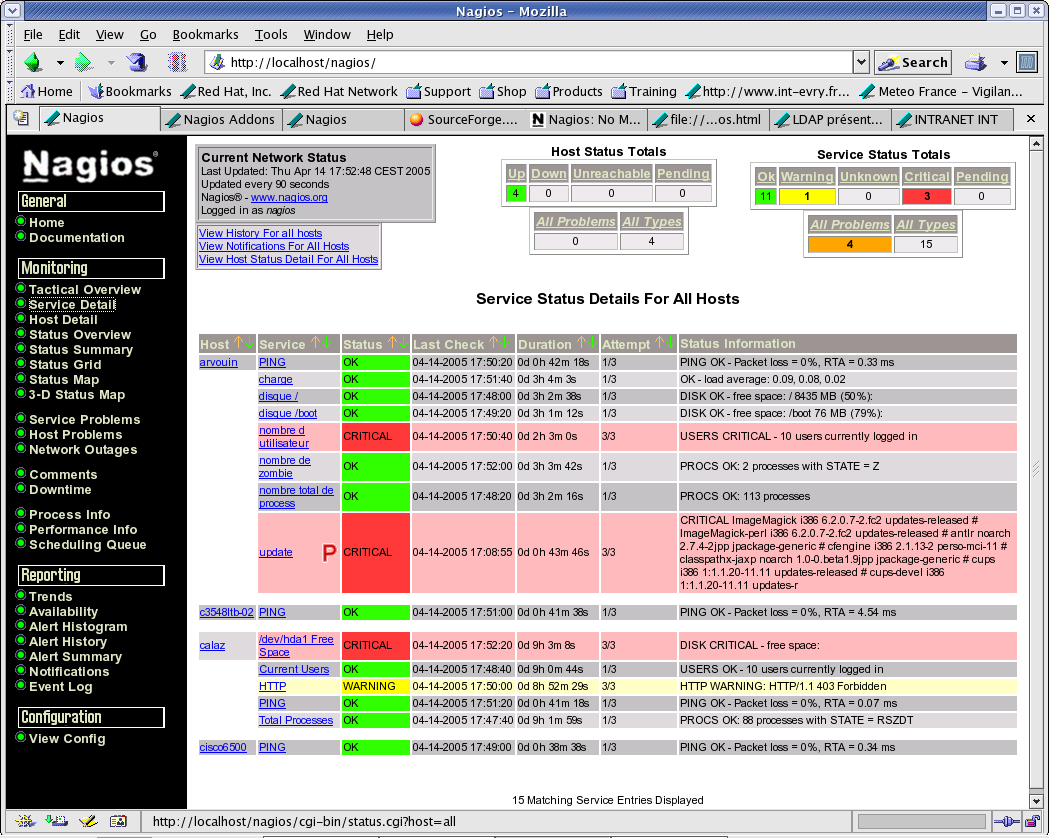
Consequences of data loss for a business are dire – downtime, lost productivity, and long-term reputational damage. Thus, organizations of all sizes need to protect their data, backup their files and computers and ensure that their systems can be restored smoothly, quickly and completely.
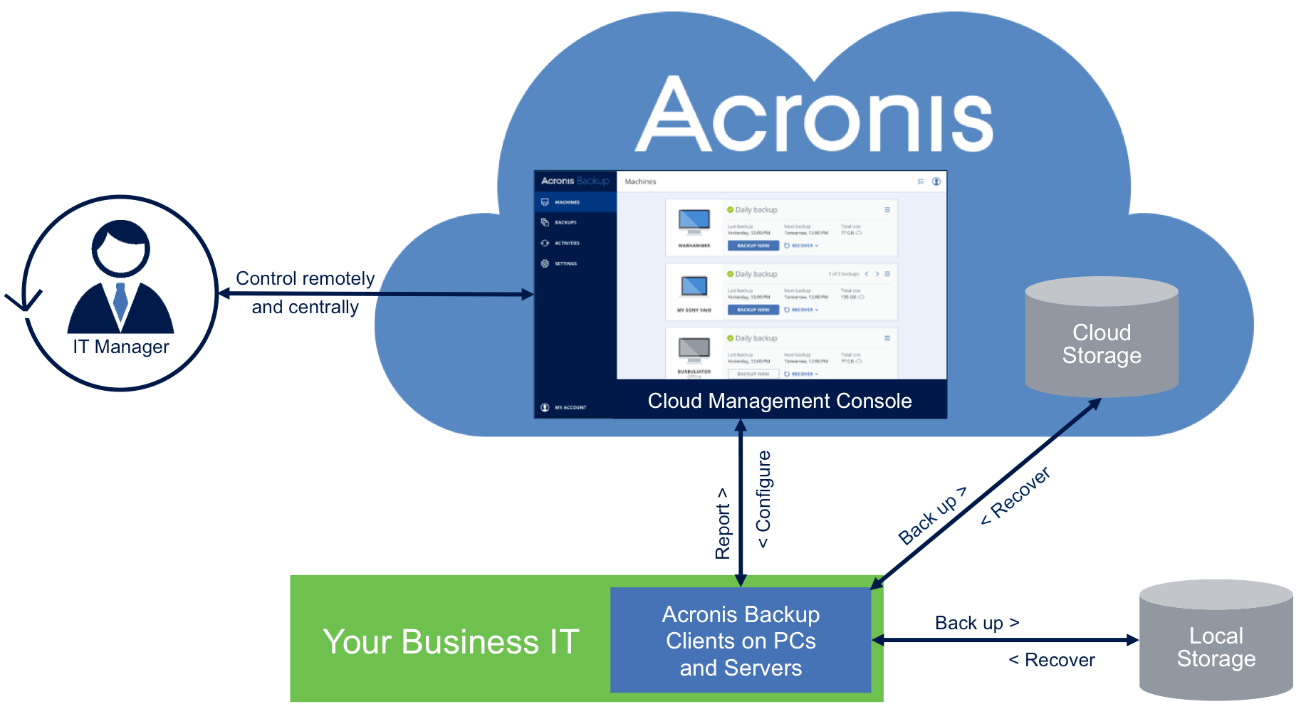
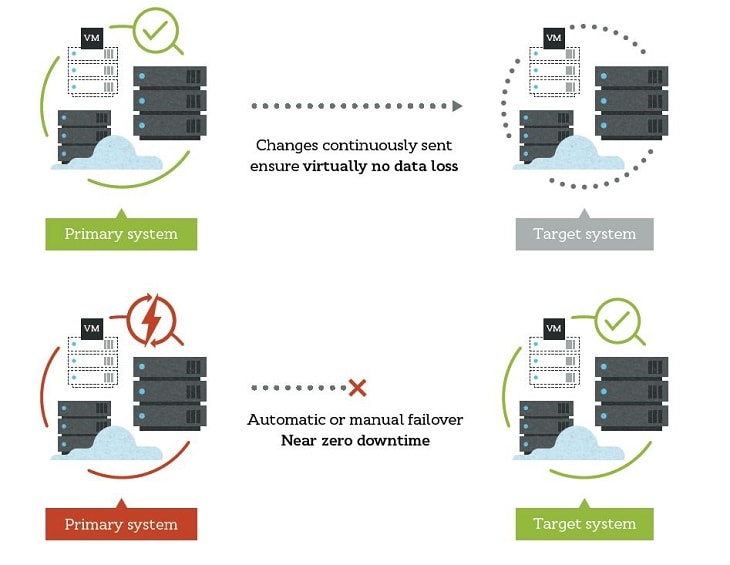
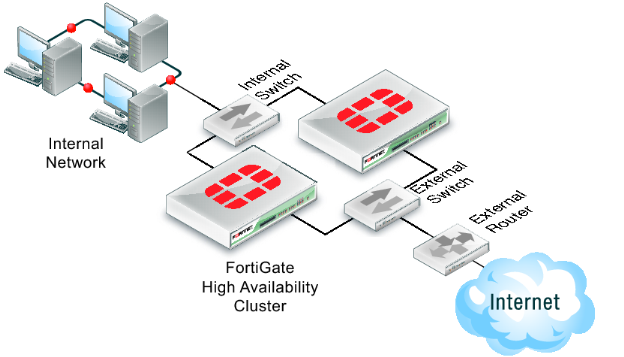
Meet your data protection needs now and in the future with easy to learn, easy to implement and cost effective, modern backup and recovery solutions. Micro Image has partnership with reputable technology brands. We can provide you backup and recovery solutions that will allow you to backup databases, enterprise applications, virtualized servers, virtual desktops, user shares, desktop data, media storage and other sources of data. Our solutions also allow easy management and protection of data on-premise or across public and private clouds. If your business fall under regulations, our solutions allow archiving that stores your backups long-term to a required retention periods for compliance purposes.